3.0 Accessibility & Usage
Upper Matter
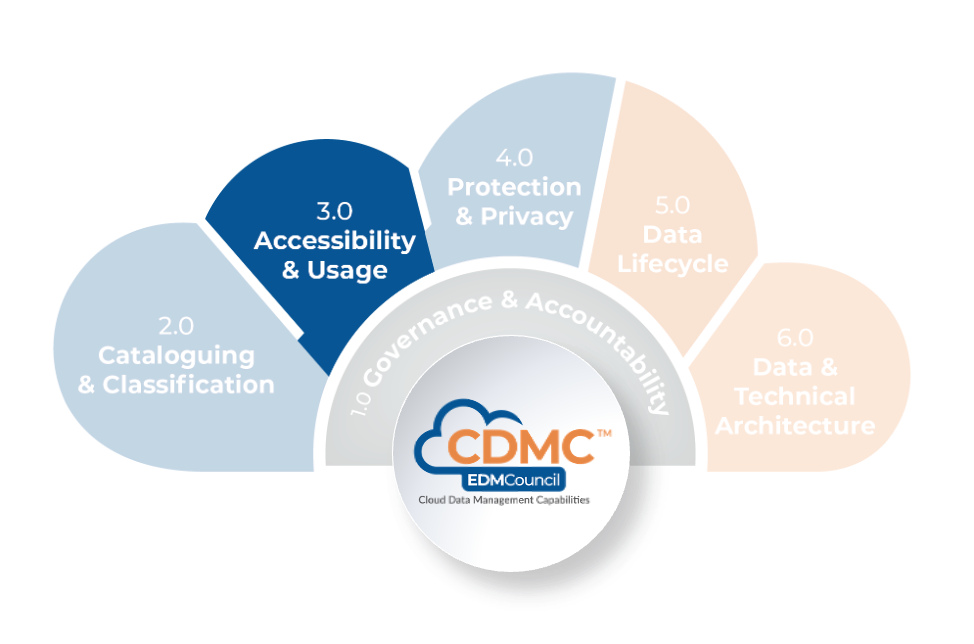
Introduction
Cloud technology offers significant opportunities for organizations to leverage their data assets in new ways. Many cloud service providers enable machine learning and advanced analytics by many more people than on-premises environments. Cloud computing technologies enable the combination of data sets in ways that were previously impracticable. When an organization seeks to maximize business value by making data and tools widely available, it is necessary to ensure that its employees can only access data to which they have proper entitlements for using that data in the organization’s service.
Description
The Accessibility & Usage component is a set of capabilities to manage, enforce and track entitlements and to ensure that data access, use and outcomes of data operations are done in an appropriate and ethical matter.
Scope
- Use metadata to express and capture the rights and obligations over data.
- Ensure that parties respect the rights and obligations over the data they are entitled to access.
- Track and report on data access for both regulatory compliance and billing purposes.
- Establish formal organization structures for oversight of data ethics.
- Operationalize ethical access and use of data and ethical outcomes of data decisions.
Overview
Understanding the data entitlement rights and obligations is critical to effective data management. The importance increases as more data assets move to the cloud. Data practitioners must provide transparency and implement controls for these rights and obligations. The adoption of cloud technology presents an opportunity for data access and use to be managed with newer, better methods. Metadata-driven data access control can be standardized and adopted to the extent that is typically not feasible in legacy, on-premises environments.
Data ethics considerations need to be addressed whether data resides on-premises or in one or more cloud environments. The need for focused attention on data ethics in cloud environments stems from the massive increase in volume, access, and use of data and the increased ability to process these data, leveraging various advanced technologies. Data in the cloud is subject to higher rates of use by an ever-increasing number of stakeholders. Organizations should develop and depend on data ethics policies and controls to ensure that these data are being acquired, accessed, and used in alignment with the organizational values and goals and the expectations of its customers.
Data entitlements
Typically, access control in legacy, on-premises environments has been addressed by entitlements frameworks that are application-oriented. Commonly, cloud computing technologies will blur, or even remove, physical and technical boundaries within and between organizations. Data—and control of data—can pass seamlessly from one party to another. A key aspect of the promise of faster provisioning in a cloud environment is the tighter connections between data producers and data consumers. Practicably, this promise can only be realized by implementing rights automation to reduce the high transaction friction associated with the licensing and permissions management necessary to provide access to data automatically.
Cloud computing lowers the technical barriers to both data distribution and Data-as-a-Service (DaaS) offerings. The ability of cloud marketplaces to support a greater variety of data, data producers, and data consumers depends on the implementation of rights automation and access tracking to:
- Offer enforcement at arbitrary levels of granularity, as determined by the data.
- Support more flexible business models like usage-based consumption.
Licensing and regulatory challenges are compounded by the need to understand and control how the rights and obligations of aggregated or derived data relate to the underlying data’s rights and obligations.
These drivers make it increasingly critical that the rights and obligations of data are described by—and move with—the data itself. Though there is additional effort to implement new systems, it is preferable to a collection of disparate, unconnected entitlements frameworks.
Cloud computing technologies offer a significant simplification and rationalization of the application and data environment to be controlled through entitlements by offering:
- Standardization and commodification of delivery, consumption, and reporting systems.
- A limited number of security and identity models, differentiated by cloud service providers rather than by individual industry actors or systems.
Metadata-driven automation enables the migration from an application-oriented entitlements framework to one focused on the data itself. Migration to one or more cloud service providers presents an opportunity to address licensing, regulatory and ethical restrictions through automated rights management.
Metadata-driven automation:
- Encourages the representation of rights and obligations as metadata.
- Emphasizes the distinction between the expression of rights and their enforcement in the data store.
- Allows the requirements for the control of data to stay with the data as it travels.
Rights automation has dependencies on lineage tracking, entitlements, metadata catalogs and reporting that can be readily satisfied by standard cloud computing functionality.
Data ethics
Data ethics is the study and evaluation of problems pertaining to algorithms, data, and information practices. The purpose of data ethics is to formulate and support morally sound solutions, such as right conduct or right values. Data ethics answers the question: How should we use and manage data?
Ethical considerations affect data management planning in two ways. First, an organization must determine what structures exist and may be used or expanded to govern data ethics. Such structural analysis should also determine who is accountable for data ethics, who has a stake in how data in the cloud is managed, and the roles and responsibilities of the stakeholders. In addition, an organization must decide how to operationalize data ethics, which includes determining the policies and processes necessary for the needed governance of data ethics.
Ethical considerations for data that resides in a cloud environment should include answering the following questions:
- How are data sourced in the cloud environment? Have both the sources and the methods of sourcing been evaluated against a code of data ethics?
- Do data agreements among data producers and data consumers explain what data is accessed, how the data will be used, by whom and following data ethics policies?
- How might data be processed with machine learning and advanced analytics? Given the growth in these methodologies, are the right policies, standards and procedures in place to ensure that ethical outcomes are being assessed and reviewed?
Data ethics considerations are independent of platform or environment. However, cloud computing introduces new opportunities and risks, presenting ethical challenges to existing policies, standards and procedures. For example, data that resides in a cloud environment may be subject to more frequent and distributed access than data stored in an on-premises environment. With increased access comes a greater risk of breach and re-identification of data subjects. Required-for-purpose data collection takes on new relevance in a cloud environment since there is a need for greater transparency. Data minimization and performing governance to ensure that the data has been collected and used correctly are essential to data management in various processes. All of the above must be documented to ensure auditability.
Cloud computing functionality can enable better control over the ethical access, use and outcomes of data, including the cataloging and auditing analytics models and their outcomes over time. Datasets used for training models may be screened for potential biases more efficiently in the advanced infrastructure of a cloud environment. In addition, an ongoing review of analytics models and their outcomes may help identify model drift—gradual change of model behavior driven by changes in the data over time—which may create ethical challenges.
Automated, comprehensive data access, use, and outcomes that are possible in the cloud environment rely on an ability to implement detailed purpose tracking and consent reconciliation. This implementation helps mitigate risk. Cloud computing features can also detect new use cases that may indicate the potential unethical use of the data.
Value Proposition
Organizations that implement metadata-driven data access control drive business value by making data readily available for innovative use while minimizing the legal and reputational risk of unauthorized access.
Organizations that achieve a culture of ethical data use and outcomes protect and enhance their business by gaining and maintaining customers’ trust.
Core Questions
- Are rights and obligations captured as metadata in a rules repository?
- Is rights enforcement automated using rights metadata?
- Are access and entitlement tracking automated?
- Has accountability for data ethics been assigned to a senior executive?
- Does a code of data ethics, data ethics working group and data ethics review committee exist?
- Have data ethics processes been operationalized?
Core Artifacts
- Rights and Obligations Catalog Report
- Data Entitlement Governance Process Documentation
- Access Logs
- Code of Data Ethics
- Data Ethics Issue Register
3.1 Data Entitlements are Managed, Enforced, and Tracked
The organization must capture data assets' entitlement rights and obligations as metadata and use this information to enforce its policies for accessing and using the data. Enforcement of data entitlements must be evidenced via automated tracking and reporting.
3.1.1 Data entitlement rights and obligations are captured as metadata
Description
Data usage is an entitlement expressly granted to authorized users. Entitlements are controlled by rights and obligations formalized in licenses, contracts, laws and regulations, business policies, codes of data ethics and data classifications. The rights and obligations must be captured and expressed in metadata as rules. To ensure consistent and reliable usage, people and systems interacting with data must adhere to these rules.
Objectives
- Develop and adopt a taxonomy or ontology for the expression of rights and obligations.
- Ensure that the requirement to capture and record rights and obligations is supported by policy.
- Capture rights and obligations as metadata in a rules repository with traceability to their source.
- Link rights and obligations to the data assets to which they apply in the data catalog.
- Ensure rights and obligations are exposed and can be consumed to support automation of their enforcement.
Advice for Data Practitioners
There are many benefits of capturing data entitlement rights and obligations as metadata.
- Enable quick, automatic compliance determinations.
- Reduce the need for third-party audits and the associated risk of fines and other liabilities created by non-compliant data usage.
- Support innovation and the ability to scale.
- Control the security and reputational risks inherent in the data processing
- Simplify change-management tasks when modifying rights and obligations for data assets.
- Ensure compliance directives propagate across platforms and applications.
- Ensure compliance directives are understood and recognized by data supply chain stakeholders and regulators.
- Reduce the cost of managing data by enhancing rights-management process automation.
Non-compliant data usage is risky and costly. Implementing rights management into an existing data governance program can significantly improve monitoring and minimize risk and cost exposures.
A clear understanding of the data entitlement rights and obligations is the first step to ensure compliance. It is necessary to acquire knowledge of the licenses, contracts, laws and regulations, business policies, codes of data ethics and classifications that control data usage. Refer to CDMC 2.2 Data Classification are Defined and Used.
Data entitlement rights are expressed as rules informed by cross-organization control functions and established by data owners. The rules define if and when data consumers can access the data. For reference, the rules should contain links to the relevant contracts, regulations or document sources.
Clarity and precision are achieved by expressing these rules as sets of:
- Permissions – what actions can be taken, such asdisplay this data to a trader.
- Prohibitions – what actions cannot be taken, such asnot sharing this data with a customer.
- Duties – the actions that must be taken to validate permission, such as areport on usage.
It is important to use a consistent vocabulary to specify permissions, prohibitions and duties. Insistence on a limited vocabulary reduces ambiguity and supports human and system interpretation. Free-text entries should be avoided.
Entitlement rules and the data assets they control are linked by articulating those rules as metadata and recorded in the data catalog. In this form, the rules allow the data management system to trace rights and obligations directly from the data itself. The permission rules function as a semantically rich directive readily acted upon by both people and systems. These directives are readily enforceable to ensure compliance. They also cultivate a common and consistent understanding of rights metadata across platforms and applications.
Expressing rights and obligations as metadata enable the automatic determination of entitlement rights. Refer to CDMC 3.1.2 Data entitlement rights are enforced, and CDMC 3.1.3 Access and entitlement tracking is automated.
To support compliant data processing along the data supply chain and beyond organizational boundaries, articulate rules with an industry-standard Rights Expression Language (for example, the Open Digital Rights Language (ODRL) market data profile).
The life-cycle of rights metadata should be managed like all sensitive metadata. Access to such metadata must be strictly controlled, and all changes must be logged and auditable. Refer to CDMC 2.1 Data Catalogs are Implemented, Used and Interoperable.
Cloud data stores enable quick discovery and access to many data assets. Understanding the data entitlement rights and obligations is critical to effective data management. The importance increases as more data assets move to the cloud. Data practitioners must provide transparency and implement controls for these rights and obligations.
Advice for cloud service and technology providers
Capturing data entitlement rights and obligations as machine-readable metadata provide broad support for automation and rapid data processing. Cloud service and technology providers should offer tools and services that enable data consumers to verify compliance before, during and after processing. Refer to CDMC 3.1.2 Data entitlement rights are enforced, and CDMC 3.1.3 Access and entitlement tracking is automated.
Preemptive compliance verification ensures that data use cases are tested for accessing the data inventory targeted for consumption. These verifications could be automated in data marketplaces, improving discovery by ensuring data consumers only receive compliant data products. In particular, entitlement rights metadata is useful in expressing data consumer requirements and data producer restrictions in a data sharing agreement.
As policies are applied along the data supply chain, data consumers may create stricter versions of the rules to reflect business policies and customer relationships. These modified rules should be testable for compliance against the original policy requirement. Refer to CDMC 3.1.2 Data entitlement rights are enforced and CDMC 3.1.3 Access and entitlement tracking is automated.
Both data producers and data consumers expect all cloud service providers to respect their entitlement rights metadata. When operating from the same metadata, compliance determinations must be identical across platforms. Cloud service providers should implement common standards for expressing entitlement rights metadata.
Questions
- Has a taxonomy or ontology for the expression of rights and obligations been developed and adopted?
- Is the requirement to capture and record rights and obligations supported by policy?
- Are rights and obligations captured as metadata in a rules repository?
- Can rights and obligations be traced to their source?
- Are data assets in the data catalog linked to the rights and obligations that apply to them?
- Can rights and obligations metadata be consumed to support automation of their enforcement?
Artifacts
- Rights and Obligations Taxonomy/Ontology definition model or document
- Data Management Policy, Standard and Procedure – defining and operationalizing capturing and recording rights and obligations
- Rights and Obligations Catalog Report – including details on the source of each right and obligation
- Data Catalog Report – tracing links to the rights and obligations that apply to each data asset
- Rights and Obligations API Specification – providing detail on how to access and use rights and obligations information
Scoring
Not Initiated
No formal capture of data entitlement rights and obligations as metadata exists.
Conceptual
No formal capture of data entitlement rights and obligations as metadata exists, but the need is recognized, and the development is being discussed.
Developmental
The formal capture of data entitlement rights and obligations as metadata is being developed.
Defined
The formal capture of data entitlement rights and obligations as metadata is defined and agreed to by stakeholders.
Achieved
The formal capture of data entitlement rights and obligations as metadata is established and adopted by the organization
Enhanced
The formal capture of data entitlement rights and obligations as metadata is established as part of business-as-usual practice with continuous improvement.
3.1.2 Data entitlement rights are enforced
Description
To be effective, an organization must enforce its policies for accessing and consuming data assets according to classification metadata, including permissions of users, groups, and applications related to data assets entitlements. Additionally, the organization must ensure enforcement of transferring data asset entitlements throughout the data lifecycle.
Objectives
- Ensure the execution of data access rights by identifying, sharing, implementing consistent enforcement of data entitlements as data travels across platforms, applications and environments—throughout the data lifecycle.
- Automate policy-based rights and permission assignment—both for data access and use.
- Automate rights enforcement according to permission metadata that derives from data catalogs and classification attributes.
Advice for Data Practitioners
An organization should explore and utilize automated cloud environment capabilities for facilitating and enforcing rights management policy as data flows into, through and outward from cloud environments. Practitioners should proactively manage and enforce data asset permissions between applications and users—throughout the data supply chain and data lifecycle.
An organization should progress to fully automatic data rights enforcement over time for all data assets. The organization should establish metadata that corresponds to each data asset. Rights enforcement that uses this metadata should support the incorporation of data ownership and transparency. Rights enforcement should also align with data governance programs and be available during policy and controls reviews.
Practitioners should ensure that authentication systems conform to the business and licensing policies of the organization. Consider proactive monitoring for entitlement discrepancies, such as varying levels of application of entitlements between applications. Also, consider establishing the ability to automate up through the highest level of entitlement enforcement to ensure compliance with policies and regulations.
Consider monitoring the consistency of each entitlement as it travels into cloud environments, various platforms and applications, and the entire data supply chain. Integrate user access controls with entitlements metadata to accelerate or automate granting, revoking or modifying entitlements.
Rights enforcement granularity should correspond to the type of data asset and guidance from the data asset owner. Commonly, an on-premises solution generally provides for rights enforcement for each application. Rights enforcement granularity should also correspond to rights management policies, which should specify the rights for each type of entity (such as database, schema, table, or data element).
Advice for cloud service and technology providers
A cloud service and technology provider should provide the capability to associate access controls with specific metadata entitlement attributes. The efficient methods that result can be readily automated. A provider should also deliver capability for the organization to an identity management system to support proactive and granular enforcement of licensing, regulatory, ethical concerns for data entitlements and data consumption.
In addition, a cloud service provider (CSP) should provide the ability to monitor and transfer data entitlements as data flows into, through and outward from the cloud environment.
Questions
- Has the enforcement of data entitlements been applied consistently and accurately to data across the data lifecycle?
- Have rights and permission assignments been automated—both for data access and use?
- Has rights enforcement been automated using rights metadata that derives from data catalogs and classification attributes?
Artifacts
- Data Management Policy, Standard and Procedure –defining and operationalizing user and group entitlements aligned to the information classification scheme
- Access Logs – evidencing the enforcement of access entitlements
Scoring
Not Initiated
No formal data entitlements rights enforcement automation exists.
Conceptual
No formal data entitlements rights enforcement automation exists, but the need is recognized, and the development is being discussed.
Developmental
Data entitlements rights enforcement automation is being developed
Defined
Data entitlements rights enforcement automation is defined and validated by stakeholders.
Achieved
Data entitlements rights enforcement automation is established and adopted by the organization.
Enhanced
Data entitlements rights enforcement automation is established as part of business-as-usual practice with continuous improvement.
3.1.3 Access and entitlement tracking is automated
Description
Data entitlements are controlled by rights and obligations formalized in licenses, contracts, laws and regulations, business policies, codes of data ethics and data classifications. Providing proof of authorized data usage requires evidence that demonstrates compliance with such rights and obligations. The evidence is especially important when collaborating with multiple internal or external parties.
To ensure compliance and enable scalable automation, it is essential to manage, enforce and track data entitlements with metadata. Moreover, it is important to record all data access events in a data access event log. Each log entry should include all users, permissions, groups, departments and applications. The level of detail must be sufficient to satisfy reporting, monitoring and compliance requirements.
Objectives
- Demonstrate adequate enforcement of entitlement rights using policy and workflow documentation.
- Record data access and track data lineage of data elements in the cloud environment.
- Support data sharing compliance, data marketplaces and data asset recommendations for analytics.
- Automate data access controls aligned with data entitlement metadata.
- Establish reporting facilities for traceability of data entitlements and data access.
- Establish outcome metrics and capture the corresponding measurements for entitlements enforcement.
Advice for data practitioners
Incorporating automated data access and data entitlement tracking can significantly reduce the ethical, business and regulatory risks of non-compliant data sharing. This tracking system must be built to minimize present and future risks by closely aligning with data privacy, ownership, sourcing, and data ethics policies. This system should provide the ability to identify all abusive patterns of data access and restrict access that is not explicitly authorized. In a cloud implementation, automatic tracking should also consider the initiation and continual evolution of data entitlements throughout the entire application lifecycle, user or departmental access to data. For example, in some circumstances, multiple data elements taken from independent sources with a lower sensitivity can—when combined—divulge sensitive personal information. In another example, a new permission scheme may enable access that violates the intent of established policies.
Explicit, deliberative and continuous tracking is essential for entitlements and access traceability. Practitioners that operate with only selective or incomplete tracking cannot rely on the sparse audit trails this produces. Such deficiencies will result in multiple data risks and security risks. Risks inevitably result in compliance failures and penalties. Organizations should implement a provider- and location-agnostic approach to data entitlement and access tracking. The approach should include the recording of all permissions changes. It should also ensure consistency in reporting across all jurisdictions, workflows, users, departments and roles.
A user access management application validates user and group permissions. It is essential to align the user access management application for permissions with access to sensitive data to maximize compliance. Access tracking should be an integral part of data lineage, and this lineage should include traceability and evolution tracking for user, departmental or role-based permissions. Refer to CDMC 3.1 Data Entitlements are Managed, Enforced and Tracked, and 6.2 Data Provenance and Lineage are Understood.
When providing evidence to demonstrate compliant data access, it is essential to have built data entitlement and access tracking into operational and compliance reporting. In addition, automation of both tracking and reporting ensures consistency and standardization.
Data entitlement and access reporting give data owners the ability to examine, assess and proactively manage risk. Reporting also provides a means to assess the value of data, verify data compliance, and consider the necessary ethical treatment of sensitive data in every context.
Advice for Cloud Service and Technology Providers
Entitlement and access tracking is important to data, policy and security management in both on-premises and cloud environments. However, the control framework may be more complex in a cloud environment, containing various hybrid and multi-cloud implementations.
Cloud environments must provide functionality for each distinct data storage entity that enables an organization and partners to:
- Manage and track the log of data entitlement classification.
- Track the evolution throughout any workflow in which sensitive data is accessed across all jurisdictions.
- Require an alert or escalation whenever logging is disabled.
- Report on data access requests in a unified, auditable, historical view, thereby detecting potential violations of organizational policies across all cloud locations and for the entire retention period.
- Run historical reports on data entitlements, access, and use compliance to support usage-based billing models.
- Integrate reporting and tracking with data marketplace environments and other mechanisms for data sharing outside the organization.
Questions
- Can enforcement of entitlement rights be demonstrated using policy and workflow documentation?
- Is data access recorded, and is the data lineage of data elements tracked in the cloud environment?
- Are data sharing compliance, data marketplaces and data asset recommendations for analytics supported with automation?
- Have automatic data access controls aligned with data entitlement metadata been implemented?
- Have reporting facilities for traceability of data entitlements and data access been implemented?
- Have outcome metrics been established that capture the corresponding measurements for entitlements enforcement?
Artifacts
- Policy, Standard and Procedure – defining and operationalizing data entitlement enforcement
- Data Access Event Log – include reporting on data access patterns, data access events and data lineage
- Functional Specifications – for automation of access controls and support of data sharing compliance, data marketplaces and data asset recommendations.
- Data Entitlement Traceability Report
- Data Access Report – including entitlements enforcement metrics
Scoring
Not Initiated
No formal automated access and entitlement tracking exist.
Conceptual
No formal automated access and entitlement tracking exists, but the need is recognized, and the development is being discussed.
Developmental
Formal automated access and entitlement tracking are being developed.
Defined
Formal automated access and entitlement tracking are defined and validated by stakeholders.
Achieved
Formal automated access and entitlement tracking are established and adopted by the organization.
Enhanced
Formal automated access and entitlement tracking are established as part of business-as-usual practice with continuous improvement.
3.2 Ethical Access, Use, and Outcomes of Data are Managed
Managing the ethical access and use of data and the ethical outcomes data use requires organization structures to be in place that focuses on data ethics. The organization must establish operational processes to report, review and address ethical issues arising from data access, use and outcomes
3.2.1 Data Ethics organization structures are established
Description
Managing data ethics for an organization has become a required discipline. Therefore, it is incumbent that organizations establish a formal data ethics oversight function, ensuring the acquisition, access, and use of data is conducted in an ethical manner and that the outcomes of data access and use are being monitored to ensure they fall within acceptable ethical guidelines.
Establishing formal organizational structures to support data ethics creates a framework and ensures ethical data access and use accountability.
Formal data ethics oversight includes a governing body, a Code of Data Ethics, and senior executive accountability with defined roles and processes. Roles and responsibilities are codified through documentation, training and verification.
Objectives
- Assign overall accountability and responsibility for data ethics to a senior executive.
- Create and enact a Code of Data Ethics for the organization as directed by the senior executive.
- Define and implement governance structures for guiding and enforcing adherence to the Code of Data Ethics.
- Identify stakeholders and form working groups to implement the Code of Data Ethics.
Advice for data practitioners
To support ethical data access and use, practitioners must identify and document data subjects’ expectations for how their data is accessed and used and evaluate outcomes of the use. As necessary, establish structures within the organization's governance functions and align those functions with the Code of Data Ethics. Governance must also support processes and protections for personnel who raise concerns about ethical data access and use.
Collaborative, routine and transparent information practices are essential to ethical data management because such practices energize the interdepartmental collaboration necessary to evolve organizational culture from being merely data-driven to being driven by data ethics.
Beginning a data ethic initiative
Early efforts to cultivate data ethics awareness in an organization typically begin with the formation of a steering committee or working group. The group communicates the principles of data ethics among stakeholders through collaborating on activities that examine the importance of data ethics through the lens of the organizational mission and values. Eventually, organizations that agree on a commitment to data ethics develop a formal, chartered data ethics governance that aligns well with the general governance structure of the organization. This governance includes a formal body of diverse stakeholders (internal and external) to oversee the ethical acquisition of data, the ethical use of data and the ethical outcomes of data use.
Realignment of the organization
The working group and the diverse formal body work collaboratively to establish data ethics compliance with the Code of Data Ethics. Such compliance should be mandated by a senior executive and implemented throughout the organization. Many organizations assign overall accountability and responsibility for data ethics to the Chief Data Officer. Implementing the Code of Data Ethics with accountability distributed throughout the organization requires data ethics governance structures that align with the overall governance structure of the organization. Examples include an ethics committee that reviews and approves new use cases. These structures allow the senior officer for data ethics to remain accountable for ethical data management for the entire organization.
Ethical outcomes
Ethical outcomes result from data access and use that meet the organization's business needs without infringing on the human dignity of others. Human dignity can be considered what society tolerates—what is generally considered fair. Organizations have a moral imperative to interrogate ethical considerations for data used to develop models and analytics—and the outcomes and effects created by their use. Ignoring such impacts on society is unethical. Governing the ethical outcomes of data access and use requires long-term scenario planning and research into the societal effects of these practices. This accountability is more complex and involved than legal compliance but also links more directly with the values contained within the organization’s Code of Data Ethics.
Going beyond mere legal compliance
The role of legal and compliance in the data management initiative is to mitigate legal risk. However, laws and regulations typically lag well behind technological change. Organizations that focus only on legal compliance risks may face costly civil and criminal challenges from data ethics risks. Legal compliance is the minimum. Innovative and responsible organizations strive to be leaders in ethical data management.
Aligning data management practices with a code of ethics
Data often contains one or more meanings. Understanding how meaning changes in different contexts and cultures is vital to ethical data management. A Code of Data Ethics describes the values underpinning an organization’s data management. When structures and processes align with the Code of Data Ethics for an organization, decision-making becomes easier since data professionals have clear guidance on ethical use and outcomes expectations.
Key principles
A Code of Data Ethics typically includes these general principles:
- Do no harm.
- Interrogate outcomes to mitigate the potential for bias.
- Ensure data use is consistent with the expectations and intentions of its data subjects.
- Collect only the data that is necessary for a specific task.
- Provide transparency—data subjects have a right to know what data is collected, how it is used and how it is shared.
- Prioritize design practices that promote transparency, clarity, comprehensiveness, explainability, configurability, accountability, and proactive interrogation of training data and outcomes patterns.
- Welcome continuous internal and external ethical review.
A Code of Data Ethics cannot explain the specific expectations or requirements for every situation. Instead, a Code of Data Ethics should provide guidance so all practitioners in an organization understand the values by which they should be making decisions about data.
A key principle of data ethics governance is the empowerment of all personnel in the organization to have the ability and the means to raise concerns about data access, use and outcomes. Practitioners must ensure procedures exist for addressing such ethical issues. In addition, there should be a way to field ethical concerns from external stakeholders as well.
Advice for cloud service and technology providers
Regulators hold an organization responsible for any cloud service and technology provider outcomes, so providers should anticipate the organization’s periodic testing and reporting to ensure that outcomes align with the data ethics expectations in the third-party agreement. In addition, providers should support the ability of the organization to document both the purposes and outcomes of data use.
Questions
- Has overall accountability and responsibility for data ethics been assigned to a senior executive?
- Has a Code of Data Ethics been created and enacted for the organization as directed by the senior data officer?
- Have operating governance structures for guiding and enforcing adherence to the Code of Data Ethics been defined and implemented?
- Have stakeholders been identified and working groups been formed to operationalize the Code of Data Ethics?
Artifacts
- Role Definitions Document – demonstrating assignment of data ethics accountability to a senior executive and outlining other roles and responsibilities
- Code of Data Ethics
- Data Ethics Governance Committee Charter – including roles and responsibilities
- Data Ethics Review Committee Charter – demonstrating diverse representation from across the organization
Scoring
Not Initiated
No formal data ethics organization structures exist.
Conceptual
No formal data ethics organization structures exist, but the need is recognized, and their development is being discussed.
Developmental
Formal data ethics organization structures are being developed.
Defined
Formal data ethics organization structures are defined and validated by stakeholders.
Achieved
Formal data ethics organization structures are established and adopted by the organization.
Enhanced
Formal data ethics organization structures are established as part of business-as-usual practice with continuous improvement.
3.2.2 Data Ethics processes are operational
Description
Operationalizing data ethics in an organization begins with a mandate from senior management, but this mandate must have broad support through specific practices and direct accountability throughout the organization. Establishing the practices and accountability is achieved through defining and operationalizing policy, standards and procedures that execute against the Code of Data Ethics established by the organization.
Objectives
- Define and approve data ethics policies for the organization.
- Deliver communication and training that reinforces the Code of Data Ethics.
- Establish a process for reviewing data acquisition, access, use and outcomes of data decisions against data ethics considerations.
- Establish a process for reporting concerns about ethical data acquisition, access, use and outcomes of data decisions.
- Establish a process for resolving ethical issues raised concerning data.
- Establish milestones, metrics and measures for quantifying the extent of adherence to the Code of Data Ethics.
Advice for data practitioners
Embedding provenance information into the metadata is one best practice that strongly supports ethical data access and appropriate data use. This approach can significantly enhance data collection and data use transparency. Another important practice is establishing tollgates in data management processes to verify adherence to the Code of Data Ethics.
It is also important that data practitioners at all levels of the organization can describe and communicate the role and responsibilities of the data ethics senior officer. Practitioners should also understand that accountability for data ethics is a data consumer responsibility throughout the organization. Understanding these responsibilities should be reinforced by investing in data ethics training and formalizing roles and responsibilities across the organization.
The organization should consider proactive measures to cultivate trust with its customers and partners. It may be necessary to provide individuals with continuous or periodic access to the data held about them beyond jurisdictions with a legal requirement. One proactive measure to reinforce a strong data ethics culture is to enhance the treatment of customer consent by collecting metadata for both legal and perceived consent. Other proactive measures include disclosing to customers the organization policy for data disposition and resolving to collect only necessary data for specific tasks.
Advice for cloud service and technology providers
Cloud service and technology providers should anticipate demand for technical solutions that help organizations and partner organizations comply with ethical obligations. Providers should also offer methods by which organizations can define, implement, and audit the purposes of data use to support ethical outcomes.
In addition, providers should have a method for documenting the outcomes of data decisions and measuring against expectations as specified in agreements. For example, proactively verifying authorized data use will strengthen relationships among the various participants in the data supply chain.
Providers should deploy automation to identify when data may be used in a new way and initiate workflows with recommendations for data owner review of new use cases.
Questions
- Have data ethics policies been defined and approved for the entire organization?
- Is there a program for communication and training that reinforces the Code of Data Ethics?
- Have processes been established for reviewing data access, data use and outcomes of data decisions against ethical considerations?
- Is there a process for reporting concerns about ethical data access, data use and outcomes of data decisions?
- Is there a process for resolving ethical issues raised concerning data?
- Have milestones, metrics and measures been established for ensuring the extent of adherence to the Code of Data Ethics?
- Have all of the above been operationalized to ‘business as usual’ for the organization?
Artifacts
- Data Management Policy, Standard and Procedure – defining and operationalizing management of data ethics
- Data Ethics Communication Plan
- Data Ethics Training Curriculum and Plan
- Data Ethics Review Process – covering ethical data access, use and outcomes
- Data Ethics Reporting Process
- Data Ethics Issue Remediation Process
- Data Ethics Metrics Report
Scoring
Not Initiated
No formal data ethics processes exist
Conceptual
No formal data ethics processes exist, but the need is recognized, and the development is being discussed.
Developmental
Formal data ethics processes are being developed.
Defined
Formal data ethics processes are defined and validated by stakeholders.
Achieved
Formal data ethics processes are established and adopted by the organization.
Enhanced
Formal data ethics processes are established as part of business-as-usual practice with continuous improvement.
3.3 Accessibility & Usage – Key Controls
The following Key Controls align with the capabilities in the Data Accessibility & Usage component:
- Control 7 – Entitlements and Access for Sensitive Data
- Control 8 – Data Consumption Purpose
Each control with associated opportunities for automation is described in CDMC 7.0 – Key Controls & Automations.
Key Control 7
| Control 7: Entitlements and Access for Sensitive Data | |
Component |
3.0 Accessibility & Usage |
Capability |
3.1 Data Entitlements are Managed, Enforced, and Tracked |
| Control Description |
|
| Risks Addressed |
Access to data is not sufficiently controlled to those who should be authorized. This could result in data leakage, reputational damage, regulatory censure, criminal manipulation of business processes, or data corruption. Data is uncontrolled and consequently is at risk of not being fit for purpose, late, missing, corrupted, leaked and in contravention of data sharing and retention legislation. |
| Drivers / Requirements |
Once the auto-classifier has identified sensitive data assets, enhanced controls should be placed on those data assets, including how entitlements are granted. The users that have access to data and how frequently they access it needs to be tracked. |
| Legacy / On-Premises Challenges |
It is difficult to track which data consumers are using which data assets unless tracking is turned on and is consistent across all the data in the catalog. |
| Automation Opportunities |
|
| Benefits |
Tracking of data consumption enables consumption-based allocation of costs. Automation can reduce the cost of performing these allocations manually. |
| Summary |
Entitlements and access for sensitive data at a minimum should be automated to default to being restricted to just the creator and owner of the data until they grant permissions to other people. Once other people have access to that data, monitoring should be in place to track who is using it and how frequently they are accessing it. Costs can then be correctly allocated. |
Key Control 8
| Control 8: Data Consumption Purpose | |
Component |
3.0 Accessibility & Usage |
Capability |
3.2 Ethical Access, Use, & Outcomes of Data are Managed |
| Control Description |
Data Consumption Purpose must be provided for all data sharing agreements involving sensitive data. The purpose must specify the type of data required and include country or legal entity scope for complex international organizations. |
| Risks Addressed |
Data is shared or used in an uncontrolled manner with the result that the producer is not aware of how it is being used and cannot ensure it is fit for the intended purpose. Data is not shared in compliance with the ethical, legislative, regulatory and policy framework where the organization operates. |
| Drivers / Requirements |
There are emerging ethical-use frameworks and guidelines that include specifications for what should happen when the use of data changes. |
| Legacy / On-Premises Challenges |
It is difficult for human capabilities to recognize when the use of data has changed into a new kind of processing that could be protected under some regulatory or legal basis without specific authorization. |
| Automation Opportunities |
|
| Benefits |
Streamlined ethical data accountability for data that is accessed for new purposes. |
| Summary |
A data sharing agreement between a consumer and the authoritative source expresses the intent to use the data for a specific purpose. Automated tracking and monitoring of data consumption purpose can alert data owners and data governance teams when there is new or changed use. |
